Introduction
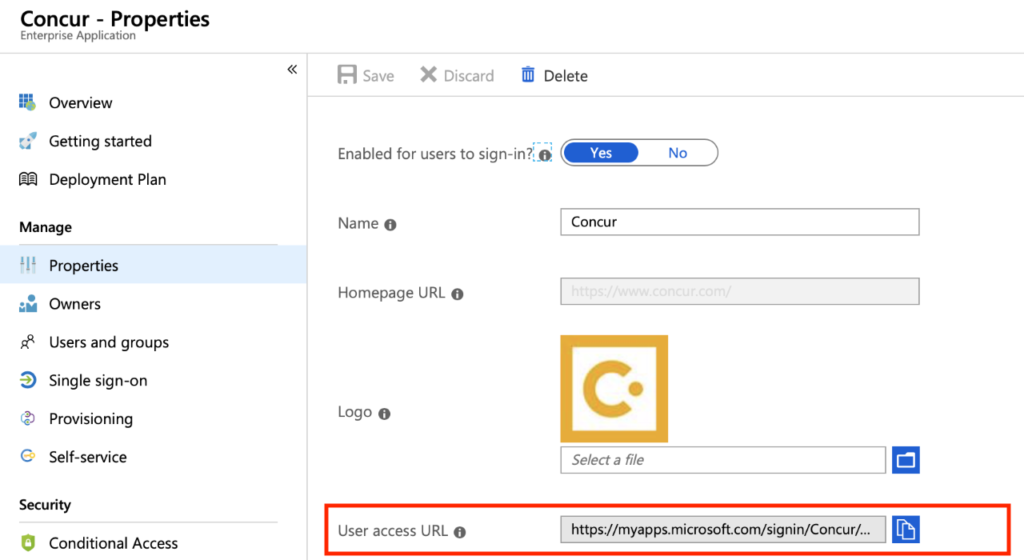
Microsoft released a new feature for Azure AD MyApps called Collections. It’s been in public preview for a little while but has released as general availability for the February identity updates. As they indicate in this article, “With the general availability of user-based collections in Azure AD My Apps, users can now create and manage their own personalized app collections while freeing IT resources and time for other tasks.”
Challenges
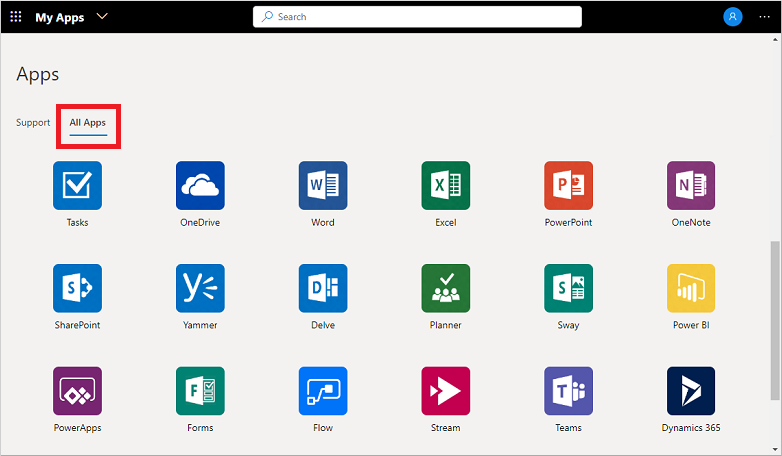
If you are on the journey of a password-less solution like the Microsoft MyApps portal to organize your enterprise applications into a Single Sign-On solution it’s common to have “app overload.” Our organization has 100+ apps now configured, with so many our users continue to ask about a way to hide or organize them. Microsoft doesn’t offer a way for users to do this, there is a way for Administrators to publish Collections to users but it is limited in its features. With the new user based collections anyone can do it themselves. Let’s take a look!
Organize your applications
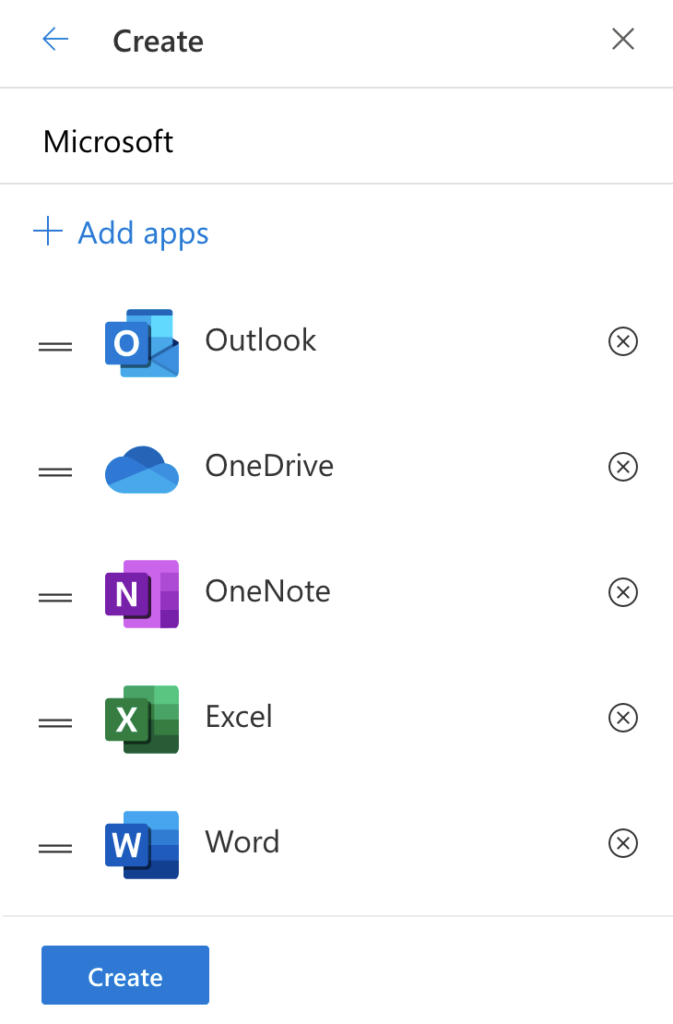
- Click on the Create button to give your Collection a name.
- Let’s add some of our Microsoft applications, you can drag and drop them in order, then click Create.
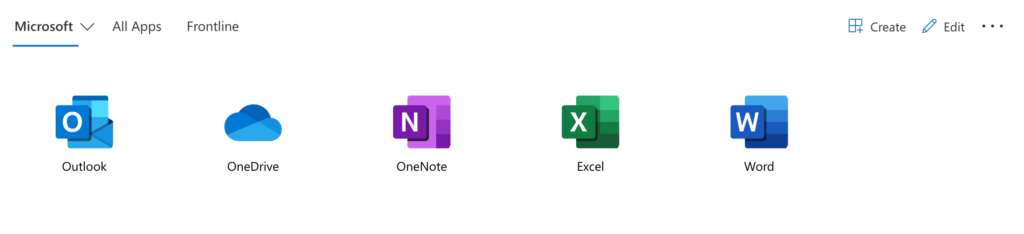
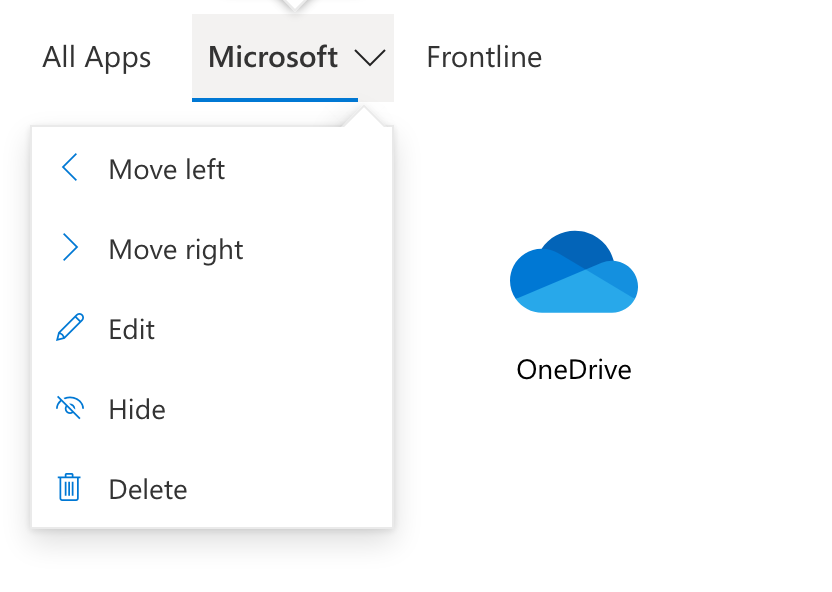
- Now you will see your new Collection. You can click the down arrow next to the Collection to make changes.
- Enjoy your new Collection!
Conclusion
This new Azure AD MyApps Collections experience is a much needed update for Microsoft. Organizing applications into different collections is a feature many other Identity solutions provide. If you haven’t started a password-less journey yet with a solutions like Single Sign-on you are missing out! Your users will rejoice with even a few applications that they don’t need to remember a username or password for. Take a look at a few other articles I have posted on MyApps and Single Sign-on.